No products in the cart.
Comparing CTEM to Traditional Risk Management
A lot of buzz has been made about Continuous Threat Exposure Management (CTEM) since the term was first coined by Gartner in 2022. As is common with the newest buzzwords and FLAs (four-letter acronyms), the real meaning and intent behind the “buzziness” can get lost in the noise. That’s certainly been true of CTEM; many articles out there will define CTEM in 50+ word run-on sentences. So, what is CTEM you ask? In an intentional oversimplification, you can think of CTEM as risk management for 2024. This article will go into more depth to give you a good understanding of what CTEM is, how it’s different from traditional risk management practices, and what hasn’t changed from 2023. More importantly, this will give you some strategies to operationalize CTEM with your clients.
Core Principles of Traditional Risk Management
Traditionally, we’ve thought about risk management as a quarterly, semi-annual, or annual exercise to evaluate the risks to the business and prioritize which risks would be mitigated in the upcoming window. That typically involves a primarily qualitative analysis to determine the likelihood and impact (potential damage) of a given thing happening. Both figures are given a number, generally on a scale of 1-5, and then the two numbers are multiplied together to get a “risk score”, where higher numbers represent more risk. Companies can then show progress as their aggregate risk scores decrease over time. With CTEM, on the other hand, the focus shifts from these point-in-time risk reviews to a continuous and real-time assessment of threats. This allows organizations to have a much more current and (theoretically*) more comprehensive view of the real risks to their organization. *We say theoretically here because you’re only going to have more thorough visibility if you have the right observability and monitoring tools in place.
For traditional risk management, there are often tried and true methods for reducing risk based on the identified and prioritized risk register. These include implementing security policies, procedures, and controls to reduce risk to acceptable levels. Note that risk doesn’t go away here, just that it gets reduced to a level that is acceptable to the business (which is another subjective measurement that is left to each business to define). CTEM takes this a step further and deploys dynamic mitigation strategies. These often include more sophisticated and adaptive approaches to preemptively prevent emerging threats.
So far, a lot of companies have focused their risk management programs on meeting regulatory requirements and maintaining compliance with industry standards. This often involves detailed documentation and periodic reporting or audits. Because of this, it is frequently time-consuming, and therefore risk reviews become infrequent and dreaded exercises. CTEM seeks to enhance compliance efforts with automated reporting and continuous monitoring. By maintaining real-time data, organizations can quickly generate compliance reports and ensure ongoing adherence to regulatory requirements.
Innovative Elements of CTEM
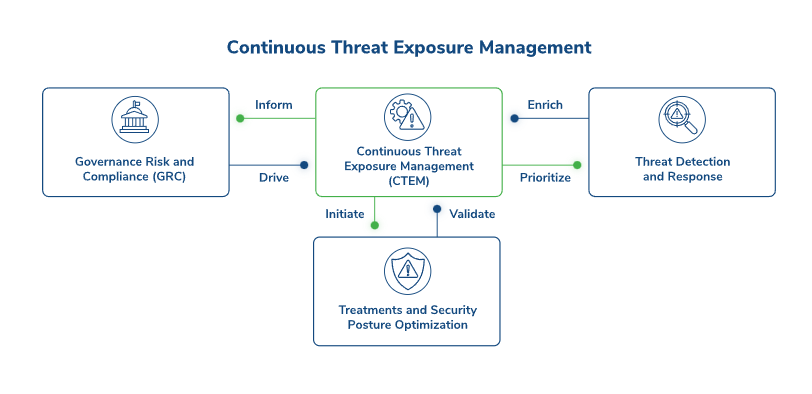
It’s important to understand that CTEM isn’t a single tool. Rather, it’s a new approach to understanding cybersecurity threats through automated and manual testing. In this way, it’s more limited than traditional risk management in that it focuses primarily on security threats. But, at the same time, it provides a more comprehensive and proactive stance towards security threats. In other words, this is not a replacement for your clients’ risk management activities, but it is a valuable enhancement. It involves many of the tools you already have in place with some innovative changes.
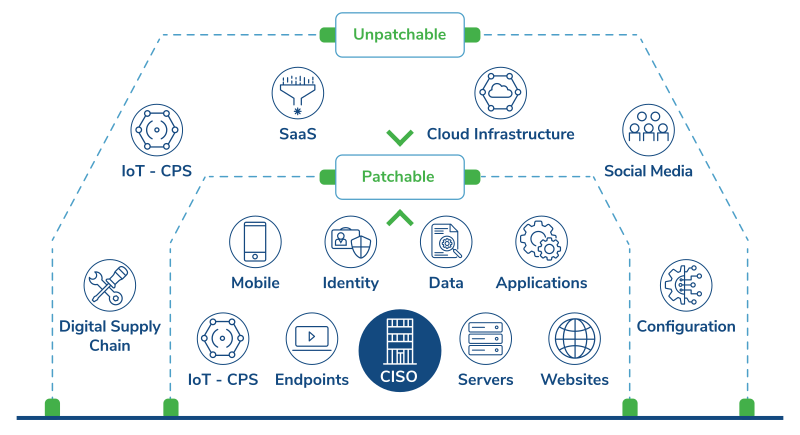
The first big piece of innovation has been discussed a little so far: it stands out with its emphasis on proactive threat intelligence. This involves continuously monitoring global threat landscapes and analyzing data to anticipate potential attacks before they occur. This specifically means looking at the macro environment, not just one client, to understand what emerging threats are. The emphasis here is not just on the number of assets or vulnerabilities, but on which of those assets are vulnerable to which types of attacks and how those attacks might play out. In other words, it’s about understanding the exploitability of the vulnerabilities rather than the quantity of vulnerabilities. This allows you to be much more proactive in adding layered defenses that make sense.
The second piece of innovation is that CTEM focuses on the continuous monitoring of systems and networks to detect and respond to threats in real-time. This is essentially taking vulnerability scans and penetration tests to the next level by automatically remediating any issues that are found. To do so, CTEM leverages advanced tools and technologies to integrate risk management into everyday operations seamlessly. Automated vulnerability assessments, real-time alerts, and centralized dashboards provide a comprehensive view of an organization’s security posture.
With more and more services moving to the cloud, patching may not even be the answer to an exploitable 0-day that affects your clients’ broader systems. This is where WAFs, VPNs, ZTNA, CSPM, SOAR, and other solutions come in. Understanding your clients’ landscape and being able to proactively apply defensive measures that make sense in the context of their systems can lower their risk profile, reduce your team’s after-hours support call volume, and reduce clients’ operational costs. These will all improve your bottom line and your client’s overall satisfaction with your services.
Source 1- https://www.kroll.com/en/insights/publications/cyber/what-is-continuous-threat-exposure-management
Complementary Aspects
As mentioned above, CTEM does not replace traditional risk management. Instead, it enhances it for security-related items.
- Policies and procedures developed through traditional risk management practices provide a foundation for CTEM. Effective policy enforcement ensures that all organizational activities align with the established security framework.
- The emphasis on creating a risk-aware culture and conducting regular training sessions is integral to both traditional risk management and CTEM.
- Incident response plans developed through traditional risk management processes are essential components of CTEM. These plans provide structured guidance for responding to security incidents, ensuring that organizations can quickly and effectively mitigate damage.
Conclusion
By understanding the distinctions and complementary aspects of traditional risk management and CTEM, MSPs can better guide their clients towards adopting a more proactive and comprehensive approach to cybersecurity. Integrating the robust elements of traditional risk management with the innovative features of CTEM ensures a more resilient security posture for each of your clients.