Surge in Brute-Force Attacks Targets Fortinet SSL VPNs
Cybersecurity researchers are warning of a sharp increase in brute-force attacks targeting Fortinet SSL VPN devices, raising concerns of deliberate and coordinated malicious activity.
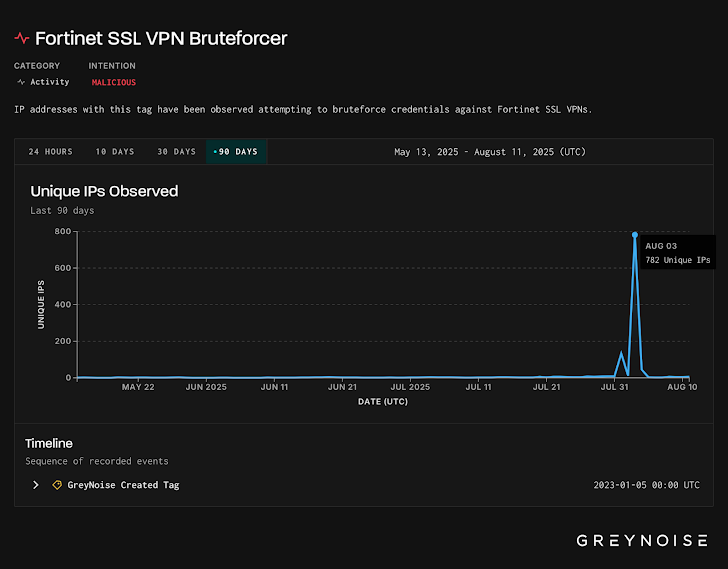
According to threat intelligence firm GreyNoise, the surge was first observed on August 3, 2025, involving more than 780 unique IP addresses. Within the past 24 hours alone, 56 malicious IPs were identified, originating from the U.S., Canada, Russia, and the Netherlands. Attack traffic has been directed at organizations in the U.S., Hong Kong, Brazil, Spain, and Japan.
“Critically, the observed traffic was also targeting our FortiOS profile, suggesting deliberate and precise targeting of Fortinet’s SSL VPNs,” GreyNoise reported, noting that the activity was “focused, not opportunistic.”
Two Distinct Attack Waves
GreyNoise identified two separate attack patterns around the incident:
- A long-running brute-force campaign tied to a single TCP signature, showing steady, persistent traffic.
- A sudden, concentrated burst of traffic with a different TCP signature, observed shortly after August 5.
Interestingly, while the August 3 activity targeted FortiOS, traffic observed from August 5 onward shifted focus to FortiManager, suggesting attackers may have pivoted their infrastructure or tools toward a different Fortinet service.
Possible Testing from Residential Networks
Further analysis of historical data revealed an earlier June spike tied to a unique client signature associated with a FortiGate device on a residential ISP block operated by Pilot Fiber Inc. This raises two possibilities:
- Attackers may have tested or launched brute-force tooling from a home network, or
- They may have used a residential proxy to obscure their infrastructure.
Broader Implications
GreyNoise noted that such spikes in hostile activity are often followed within six weeks by the disclosure of a new vulnerability (CVE) affecting the targeted technology. These trends have been observed most often with enterprise edge systems such as VPNs, firewalls, and remote access tools — critical assets that advanced threat actors frequently target.
The findings were detailed in GreyNoise’s latest Early Warning Signals report.